Security of any WordPress site involves a huge array of factors. But one of the most critical of these is protection of user accounts and particularly those of administrators.
Adding multiple layers of protection for your user accounts is crucial to account integrity. It helps ensure that anyone or anything who shouldn’t be inside your site, never gets in.
In this article we will show you how easy it is to protect your WordPress login in 3 different ways, from those that would try to brute force their way through.
What is “limit login attempts”?
Limit login attempts is where you put a maximum on the possible number of attempts that a bot, or other bad actor, is able to make to log into your site.
The more times a bot can attempt a login, the greater chance they have to correctly guess a password.
With enough tries, a bad actor could eventually guess a password correctly and gain access, especially if password policies aren’t enforced.
Here are the easy ways to limit login attempts on WordPress
The Shield Security Pro plugin comes with numerous ways to limit login attempts, and they fall under the following 3 approaches:
- limit the total possible login attempts that a site will process.
- detect automated bots and reject their login requests.
- detect multiple failed login attempts from 1 location (IP) and block further access.
Each of these approaches have advantages and disadvantages, but combined, they present the most powerful set of tools available to limit login attempts to your site.
We’ll take each in detail, show you how it works, and how to enable it.
#1 Limit Maximum Login Attempts On A Site
If you can place a hard, upper limit on the total maximum number of attempts to guess a password, then you dash all hopes of ever guessing any passwords.
Imagine your website can process 20 login requests per second. That equates to ~52 million requests in a month – that’s a lot.
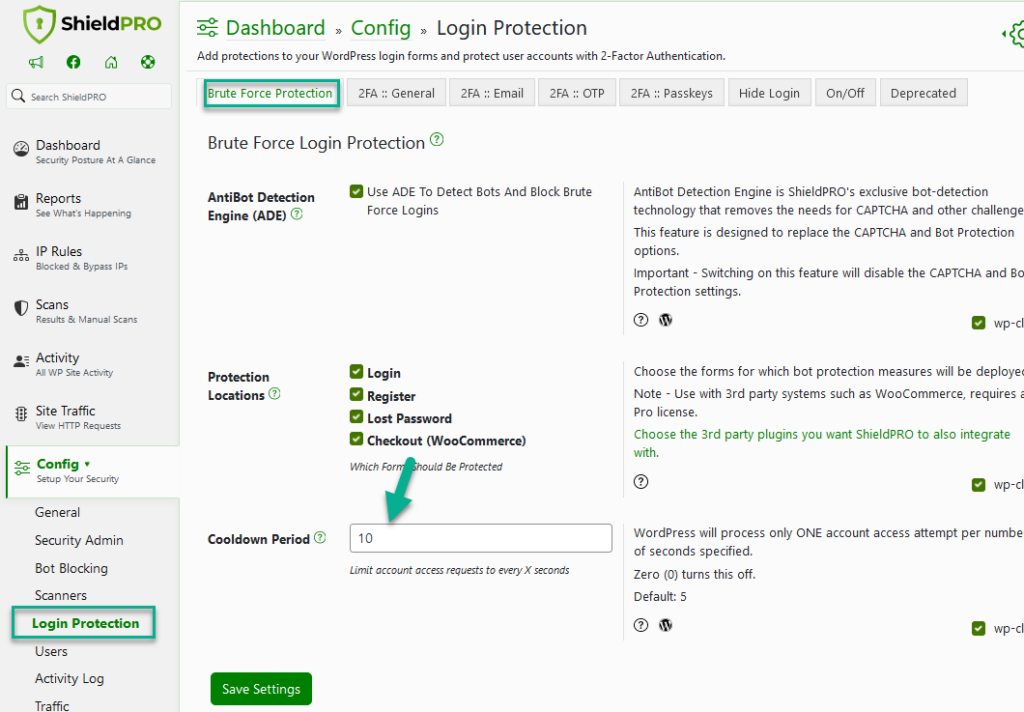
What if you could set it so that WordPress wont even try to authenticate a login, if one was already tried in, for example, the last 10 seconds?
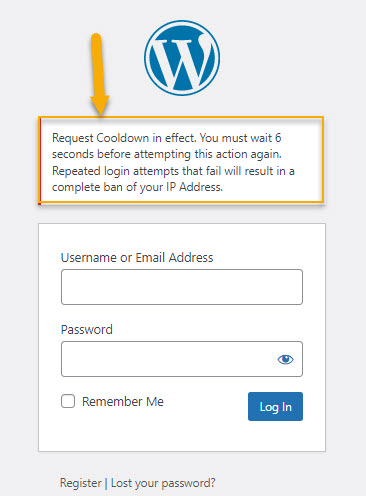
We call this a ‘cooldown’ system, where absolutely no logins will be processed during the 10s cooldown period.
So instead of 200 tries in 10 seconds, you permit only one. That changes the maximum possible requests to: ~260K in a month. Still large, but significantly less than before: 0.5% when compared to without a cooldown.
And you can increase the size of the cooldown to more than 10 seconds, and this limits the maximum possible tries even further.
The stunning beauty of this approach is that there’s no special code, or bot prevention javascript needed. It’s all transparent to your users.
How To Set A Login Cooldown Using Shield Security Pro
#2 Detect Bot Requests and Reject Them Immediately
With a cooldown in-place, you’re already protecting against bot requests, but we can go even further.
Using the characteristics of bots, we can add a few elements to the login form that helps us identify bot requests as they come through.
This will nearly always cause a little bit of friction for the legitimate visitor, but our goal is to strike a balance between increasing security and detracting from the user experience.
Thankfully Shield has 3 ways to achieve this smoothly:
- login honeypot – where we add a hidden field, unseen by the normal visitor which, if filled-in by the bot, simply means they’re a bot
- AntiBot Detection Engine (ADE)
- the “I’m a human” checkbox
Option 1 is completely transparent to your users, so it has no cost in user experience. It is, however, common practice and most bots can work around it. But we keep it in there to be complete as there’s zero impact to the user experience.
Option 2 is a best and highly effective way to detect Bots and block Brute Force logins.
AntiBot Detection Engine is ShieldPRO’s exclusive bot-detection technology that removes the needs for CAPTCHA and other challenges.
Option 3 is one of the effective ways of detecting bots and only asks legitimate visitors to check a single checkbox.
Note: This option is depreciated. You can still use it but we highly recommend using ADE instead.
#3 Block IP Addresses After Detecting Multiple Failed Login Attempts
The previous 2 approaches deal with independent requests. They make no consideration for whether repeated login attempts came from the same place.
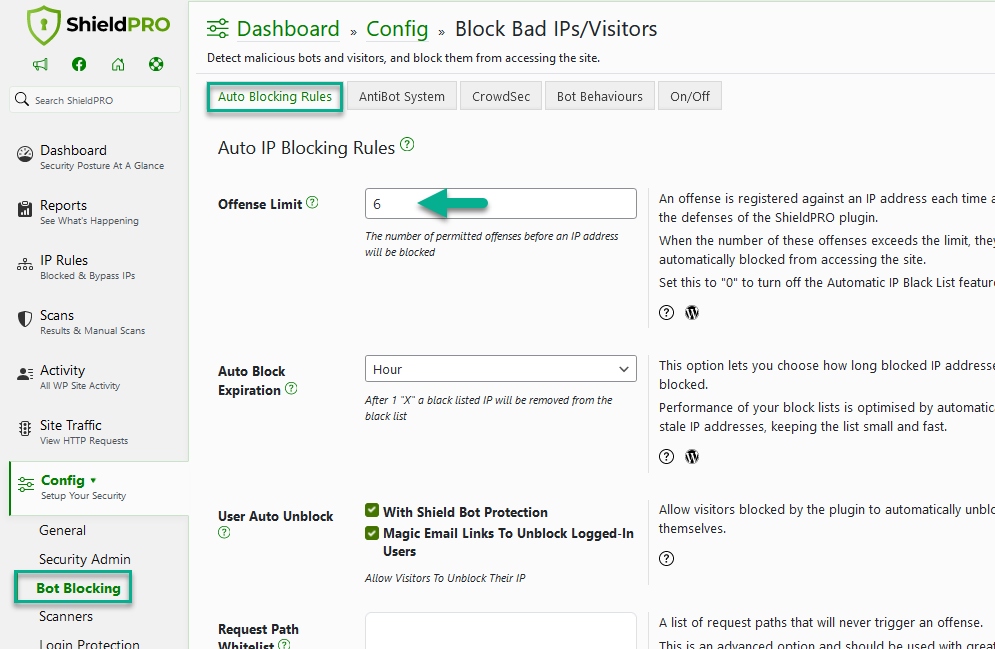
Since we’re now looking at the IP address of the failed login attempts, and if we spot more happening than we’d like, we block the IP address so they can’t try again.
Shield Security Pro uses the term “offense” to refer to “bad” actions taken by a visitor. Each time a visitor does something we don’t like, we increase their offense counter.
When that counter exceeds our limit, the IP address is blocked by Shield.
In this simple way, we can limit not only login attempts, but access to the site altogether.
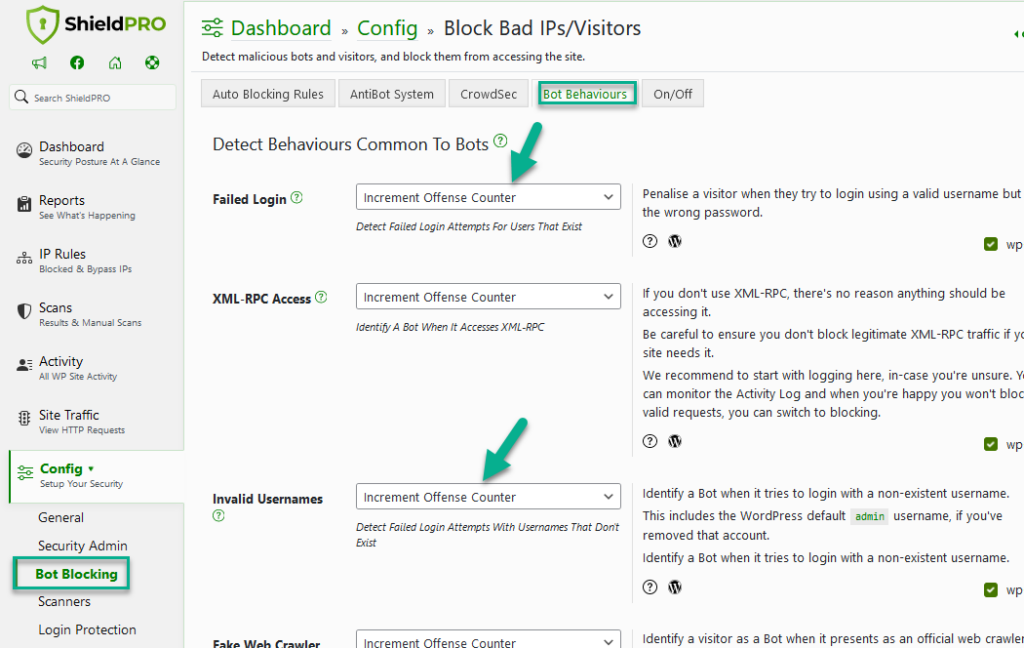
How To Ensure Login Attempts With IP Address Blocking
It worth noting that with Shield you can handle the different types of failed logins however you want to.
If you think about it, there’s a difference between a failed login attempt when it uses a valid username, compared to if a non-existent username was used.
With Shield, you can decide exactly how to handle each situation. You can increment the offence counter, you could log it in the activity log, or you could even block the IP immediately.
We leave this decision up to you because you know your sites best.
How will you know if it’s working?
You may have noticed that Shield doesn’t send you emails all the time. Does this mean it’s not doing anything?
Not at all.
You see, an email represents a huge tax on your time. Each time you receive one, you need to:
- see it
- open it
- read it
- process it
- care about it
- do something about it
Do you really have time for that? Wouldn’t you prefer your security services to just … handle it and leave you alone?
Of course you would. We certainly do, and that’s why we built Shield Security the way we have. We want Shield to be intelligent and automate as much of the hard work as possible, without bothering us about any of it, unless it’s absolutely necessary.
And the same applies here. When Shield blocks a nefarious login attempt, it logs it, and it wont bother you with it. The purpose is to protect your sites after all, it doesn’t need to show off.
Soon, with Shield 7.5, we’re going to amp-up our logging and statistics, so you’ll be able to see everything that goes on under-the-hood, and get the numbers on it too.
Conclusion and Summary
We’ve presented the powerful ways Shield lets you limit login attempts to WordPress. They each have their advantages over the others, but when combined together, they present the strongest login protection available.
All of these settings can even be applied to WordPress user registration and forgotten password requests.
There’s absolutely no reason to leave your WordPress login and registration pages open to attack and abuse.
Hello dear reader!
If you want to level-up your WordPress security with ShieldPRO, click to get started today. (risk-free, with our no-quibble 14-day satisfaction promise!)
You'll get all PRO features, including AI Malware Scanning, WP Config File Protection, Plugin and Theme File Guard, import/export, exclusive customer support, and much, much more.
We'd be honoured to have you as a member, and look forward to serving you during your journey towards powerful, WordPress security.